Today we will root two boxes from HTB that are so similar that the same techniques can be used. The boxes are the Grandpa and Granny. Also we will escalate our privilages with two different manual ways Initial foothold PrivEsc with Churrasco PrivEsc with MS14-070 As always we start the scan with nmap We see…More
Category Archives: Windows
HTB – Optimum Walk-through
Today we will root manually Optimum Box. Let’s see how We scan the machine We see that only one port is open, port 80. If we navigate there we see that an HttpFileServer httpd 2.3 is running. If we search the exploit-db we see this A remote command execution script. So we will use this…More
HTB – Jerry Walk-through
Today we will root manually the Devel Box. Let’s see how We scan the machine The only service that this machine has is an Apache Tomcat service. If we visit the ip on that port we do not see anything useful. As we know that this is a tomcat server we can visit the /manager…More
HTB – Devel Walk-through
Today we will root manually the Devel Box. Let’s see how We scan the machine We have two ports open, a ftp service which allows anonymous logins and also to upload files and a http server that doesn’t host anything. From the descriptions of the ftp files we can suspect that this server might run…More
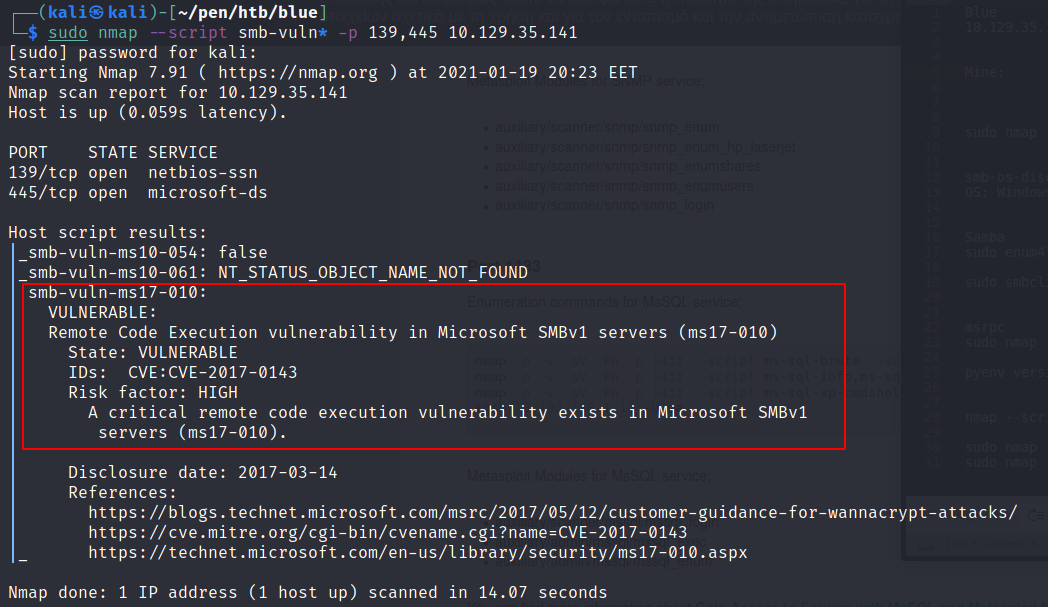
HTB – Blue Walk-through
Today we will root with metasploit and manually the Blue Box. Let’s see how First we do our usual scan We see multiple ports open but the most interesting is the smb service. Before we enumerate smb we check also the msrpc service with the nmap script engine. But there is nothing interest from the…More
HTB – Lame Walk-through
Today we will see how to root the Lame box, so let’s start We start with the usual port scanning The most interesting ports are the smb service (139,445) and the ftp (21). At first we see that the version of smb is 3.0.20-Debian and is a linux box. We also see that the ftp…More
HTB – Legacy Walk-through
This is my first walk-through for a very old machine from Hack The Box page. Also this is my first box 🙂 We will see how we can root it both with metasploit and manually. At the time this blog post was written, Python 2 has reached EOL and is no longer being maintained in…More